标签:files 20 Attacks up eric Penetration ls txt easier
Persistence and Stealth
PERSISTENCE
- Scheduled jobs
- Cron or Task Manager
- Scheduled Task
- Same as above
- Daemons
- Background processes or services
- Back doors
- Bypass standard security controls
- Trojan
- Malware that looks like it does something useful
- New user creation
- Makes later logins easier
STEALTH
- Clean up files, including tools installed
- Hiding files that you need to leave
- Sanitize log files (remove entries or entire logs)
- Remove any traces of activity while accessing the environment
DEMO
ls ls -l ls -al
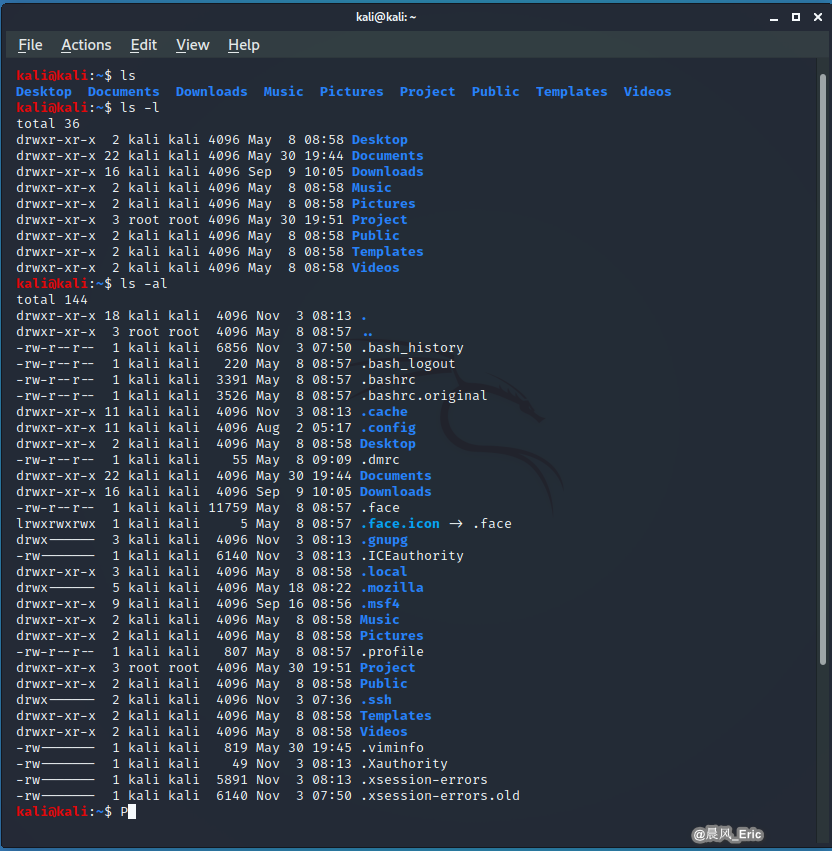
Hide a file by adding a dot to the beginning.
touch eric.txt
mv eric.txt .eric.txt
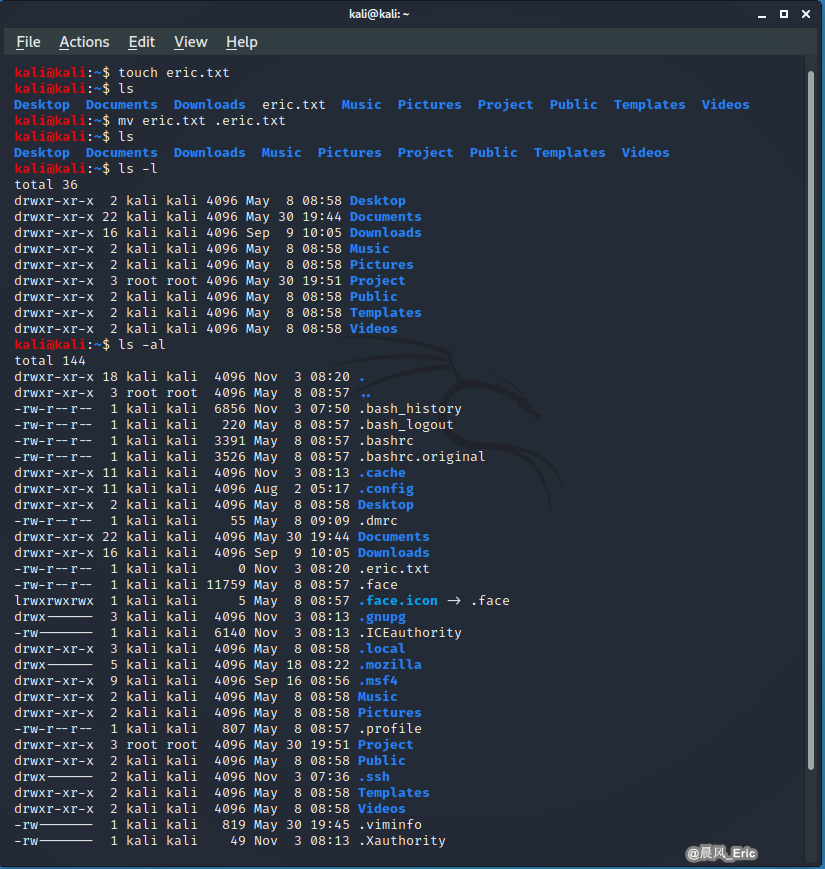
Easy to find the hidden file using ls -al or cat command.
cat .bash_history
QUICK REVIEW
- Set up persistent processes to maintain a presence
- Install low profile tools and malware to make your job easier
- Leave artifacts that keep the attack going and make it easier to get back in
- Once the attack is over, clean up to avoid post-mortem detection
标签:files,20,Attacks,up,eric,Penetration,ls,txt,easier 来源: https://www.cnblogs.com/keepmoving1113/p/13922686.html
本站声明: 1. iCode9 技术分享网(下文简称本站)提供的所有内容,仅供技术学习、探讨和分享; 2. 关于本站的所有留言、评论、转载及引用,纯属内容发起人的个人观点,与本站观点和立场无关; 3. 关于本站的所有言论和文字,纯属内容发起人的个人观点,与本站观点和立场无关; 4. 本站文章均是网友提供,不完全保证技术分享内容的完整性、准确性、时效性、风险性和版权归属;如您发现该文章侵犯了您的权益,可联系我们第一时间进行删除; 5. 本站为非盈利性的个人网站,所有内容不会用来进行牟利,也不会利用任何形式的广告来间接获益,纯粹是为了广大技术爱好者提供技术内容和技术思想的分享性交流网站。
